
The traditional barricades of firewalls and encrypted tunnels are no longer enough to protect a society where a language model's logic dictates the security of physical infrastructure. While the industry spent decades perfecting the art of patching broken code, the rise of sophisticated AI agents

The sheer velocity of modern computation has reached a point where yesterday’s supercomputers now look like relics compared to the specialized engines driving today’s generative breakthroughs. As industries move beyond the experimental phase of artificial intelligence, the collaboration between

The silent hum of a power grid or the steady flow of a city water system represents the invisible heartbeat of a modern nation, yet these vital systems are increasingly finding themselves in the crosshairs of sophisticated digital aggressors. Critical national infrastructure consists of the

The rapid disintegration of the traditional corporate network perimeter has forced a fundamental reconsideration of how digital assets are protected in an increasingly volatile global landscape. For over a decade, security professionals relied on the assumption that anything inside the firewall was
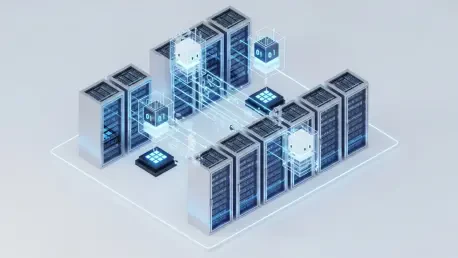
The rapid proliferation of autonomous artificial intelligence agents within corporate infrastructures has fundamentally dismantled the traditional boundaries of network security by introducing entities that act with the agency of human employees while maintaining the processing speed of silicon.

The rapid integration of artificial intelligence into every facet of the corporate world has created a fascinating paradox where the velocity of innovation often outpaces the structural integrity of the systems hosting it. While the promise of automated efficiency dominates the headlines, a more
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24