The digital fingerprints of thousands of global enterprises vanished into a metaphorical black hole this month, leaving a void where a billion-dollar economy once hummed within the Middle East’s most advanced cloud corridor. When the AWS ME-CENTRAL-1 region suddenly dropped off the global map in March, the immediate concern was the loss of service; however, the unfolding reality is far more destabilizing for the modern enterprise. Organizations attempting to perform their end-of-month audits have discovered that the servers they paid for, the data they moved, and the infrastructure they managed have been systematically scrubbed from the provider’s official history.
This unprecedented erasure represents a fundamental shift in how the industry understands cloud risk and the reliability of digital record-keeping. For years, the cloud bill has served as the “canonical record”—the undisputed source of truth for what a company owns and operates in the ether. By zeroing out usage metrics following a catastrophic regional failure, AWS has not just provided financial relief; it has effectively deleted the evidence of a month’s worth of operations. This decision forces a confrontation with a uncomfortable truth: the history of a business’s digital existence is entirely at the mercy of the provider’s administrative discretion.
The Vanishing Act: Middle East Control Plane Failure
The silence emanating from the ME-CENTRAL-1 region was not the result of a standard software bug or a localized power failure, but a total systemic collapse that paralyzed the administrative layer of the cloud. When the control plane failed, it took with it the ability for customers to see, touch, or stop their running resources. Engineering teams found themselves in a digital purgatory, watching from afar as their infrastructure remained unreachable, yet presumably still active, within the failing data centers.
This collapse meant that the very tools used to manage “dead” resources were themselves casualties of the event. While typical outages involve a loss of connectivity, this incident saw the absolute disintegration of the telemetry systems that track usage. Without these heartbeat signals, the central nervous system of the cloud could no longer account for the state of the hardware. Consequently, the granular data that typically informs a company’s Cost and Usage Report (CUR) simply ceased to exist, creating a vacuum in the middle of a high-stakes operational period.
Why the UAE Incident Redefines Cloud Risk
The events in the United Arab Emirates demonstrate that the physical safety of a data center is no longer a secondary concern for IT leaders, especially as geopolitical tensions boil over into kinetic conflict. Most disaster recovery strategies are designed around the concept of “five nines” of uptime and the resilience of software-defined networks. However, when the risk shifts from a fiber cut to the physical destruction of multiple availability zones by state actors, the existing playbooks become obsolete. This is the first time a major provider has had to navigate the total loss of infrastructure due to military action, and the precedent being set is one of total data sanitization.
Furthermore, this incident highlights the extreme dependency that global organizations have on the provider’s billing engine as their primary inventory tool. When that engine is retroactively modified, it disrupts the internal governance of every customer in that region. The realization that a provider can—and will—alter the historical ledger to simplify a PR or support crisis introduces a new “black swan” variable into risk assessments. It suggests that the digital trail of an organization is far more fragile than the physical assets it replaced.
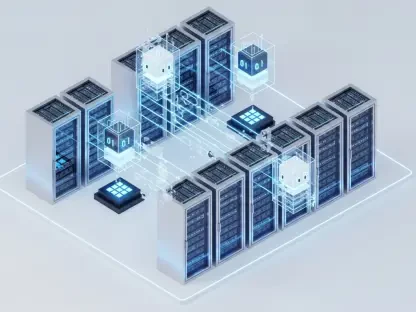
Anatomy: Regional Collapse and the Corporate Response
The technical failure was triggered by the physical loss of two out of three availability zones, which immediately rendered 109 independent services non-functional. Because AWS architectures are designed for high availability across zones, the sudden, violent removal of the majority of the region’s footprint created a cascade of errors that the control plane could not resolve. Metadata about running instances was lost in the rubble, making it impossible for the provider to deliver a standard billing report that reflected reality.
In the aftermath, the corporate response from AWS focused on a “diplomatic” waiver that prioritized customer satisfaction over historical accuracy. By choosing to waive all charges for the month, the provider avoided a logistical nightmare involving millions of disputed line items for services that customers couldn’t access. However, this move also served to obscure the scale of the disaster. By issuing a blanket zero-dollar statement instead of a credit against a documented balance, the company bypassed the need to record the failure of specific services in the official usage logs.
Disappearing Truth: Impact on Governance and Security
Security and compliance officers are now facing a forensic nightmare, as the tools they use to verify a company’s security posture rely on the very logs that have been deleted. A cloud bill is often the only way an auditor can verify that a specific database was running with the correct encryption settings or that a firewall was active during a specific window. With the usage data scrubbed, there is no longer a digital trail to prove that compliance standards were met during the chaotic weeks of the collapse.
This “clean slate” approach to billing sets a troubling precedent for the integrity of corporate records. Analysts argue that by allowing a provider to “un-happen” a month of activity, the industry is moving toward a model where transparency is sacrificed for operational convenience. If the official record shows zero activity, but a company’s internal logs show a massive data breach occurred during that same period, the discrepancy could lead to legal and regulatory complications that last for years. The sanitization of the ledger effectively removes the context needed to understand the true impact of the regional failure.
Navigating the Reality of Regional Vulnerability
The shift toward total regional vulnerability requires organizations to rethink the traditional “all-in” cloud strategy that has dominated the last decade. It is no longer sufficient to rely on a single geographical hub, even one as sophisticated as the UAE, without a secondary control plane located in a different geopolitical theater. Companies must begin to treat “Regional Conflict” as a top-tier risk item, ensuring that their recovery plans do not assume the continued availability of the provider’s management console or historical usage data.
To protect against future erasures, enterprises should implement independent, off-region telemetry and inventory logging that exists outside the provider’s primary billing environment. By maintaining a third-party record of resource metadata, a business can preserve its own version of the truth even if the provider decides to wipe the official ledger. The lesson of the UAE collapse was clear: while the cloud offers immense scale and flexibility, it also grants providers the power to rewrite history, making self-recorded forensics a mandatory requirement for any organization operating in a volatile global landscape. Independent logging and multi-region governance are now the only ways to ensure that an organization’s digital footprint cannot be erased by a single executive decision or a kinetic strike.
The fallout of the UAE regional collapse showed that the cloud’s promise of permanence was an illusion. Organizations realized that their operational history was a hosted service, just like their databases, and it could be retracted at any time. Security leaders adjusted by treating provider-side logs as secondary evidence rather than absolute truth. Governance teams established new protocols to mirror metadata across multiple continents, ensuring that even if a region was wiped from the map, the record of its existence remained secure. The industry moved toward a more cynical, yet more resilient, model of digital sovereignty where the responsibility for historical integrity rested solely with the customer.