Boardrooms confronted with cross-border subpoenas, shifting sanctions lists, and sudden export controls are redrawing cloud maps overnight to keep core systems resilient and within reach of domestic legal protections. That urgency has a name: geopatriation—the deliberate relocation of sensitive data and applications from global public clouds to local or regional environments that promise enforceable control. The pivot is not about abandoning scale; it is about asserting jurisdictional clarity and operational continuity when a single vendor’s legal exposure spans multiple flags. Analysts describe a measured, durable shift that trades one-size-fits-all architectures for portfolio thinking, where sovereignty, portability, and exit paths become first-order design inputs alongside cost, latency, and developer velocity.
Why Geopatriation Is Accelerating
Regulatory momentum turned abstract policy into procurement criteria. Governments tightened rules around data handling through instruments such as GDPR, NIS2, the EU Data Act, and sectoral mandates that specify locality, lawful access, and operational oversight. Gartner projected that up to 20% of IaaS workloads would move to local providers by 2027, and that by 2028, 65% of governments would set digital or technological sovereignty requirements. The driver was not paperwork alone. Extraterritorial laws, including the U.S. CLOUD Act and equivalents elsewhere, created uncertainty about compelled access. That prompted risk leaders to seek verifiable controls: auditable chains of custody, clear processor responsibility, and the ability to ringfence operations.
The geopolitical backdrop reinforced that trajectory. Export restrictions on advanced semiconductors, tightening scrutiny of cryptography, and data-transfer disputes exposed fragile assumptions about frictionless cloud consumption. Enterprises with operations spread across the EU, the Gulf, and Asia-Pacific needed strategies that could withstand diverging lawful access regimes and localization laws from India’s DPDP to China’s CSL. The result was a shift in board-level expectations: cloud strategy had to evidence control, not just agility. That reframing elevated questions once buried in appendices—who operates the service, which entity can be compelled, what escalation path exists if borders harden—into gating criteria for workload placement.
From Reaction to Architecture
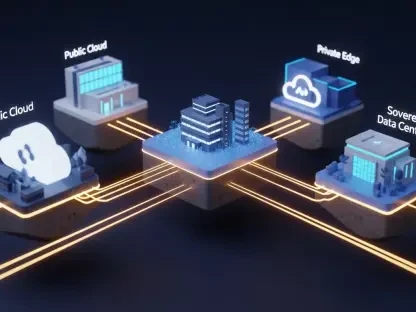
Forrester’s view—sovereignty as an architectural shift—has been borne out in reference designs now taking shape in procurement documents and platform roadmaps. Rather than panic-migrating everything, organizations mapped sensitivity tiers and codified placement policies. Highly regulated datasets, such as public-sector registries or core banking ledgers, moved toward sovereign or jurisdictionally insulated environments. Less sensitive analytics, burst rendering, and dev/test stayed on mainstream public cloud, tethered by stricter guardrails. The change showed up in patterns: control planes deployed locally, encryption with customer-held keys, policy engines that enforced processing location, and CI/CD pipelines tested for portability on day one.
Building on this foundation, architecture teams embraced incrementalism as a hedge against lock-in. API-level compatibility and open formats—Kubernetes, OpenTelemetry, S3-compatible object storage, HashiCorp-compatible workflows—were favored to keep exit options live. Procurement clauses demanded practical portability: documented restore procedures, verified data egress paths, and penalties for undue friction. The outcome was less glamorous than a wholesale reset but far more durable. It preserved access to hyperscaler innovation where appropriate while creating hard boundaries for critical workloads. In this model, sovereignty was not a destination but a gradient applied per system, enforced by policy and validated through audits.
Workloads and Operating Models
The first movers were high-sensitivity, business-critical systems where lock-in and exposure carried existential risk. Core payment rails, patient records, defense telemetry, and identity services gravitated toward local sovereign IaaS that could underpin compliant PaaS and SaaS layers. Gartner linked this stack-aware pattern to risk reduction: when the base infrastructure complied with locality and operational separation, higher layers inherited stronger assurances and clearer recourse. In EMEA, the tilt gathered pace; by 2030, Gartner expected more than three-quarters of enterprises in Europe and the Middle East to shift some or all virtual workloads locally, aligning procurement with national cloud certifications and sectoral playbooks.
Operating models evolved in tandem. Private cloud modernized through Kubernetes distributions with FIPS-validated crypto and confidential computing on domestic hardware. Colocation anchored data residency in accredited facilities, with sovereign key management and customer-operated HSMs. Hybrid designs stitched on-premises control to public elasticity via service meshes that respected policy boundaries. Multi-cloud diversified dependency, using cloud-native gateways to route by jurisdiction and fail over without violating residency constraints. The technical glue was open standards: SPIFFE identities for workload attestation, OPA for policy, SBOMs for software provenance. Together, these tools translated governance into repeatable pipelines rather than ad hoc exceptions.
The Market: Convergence, Trade-offs, and Next Steps
Market responses converged from both ends but remained uneven in substance. Hyperscalers launched sovereign regions, isolation controls, and partnerships with domestic operators to address legal exposure. Some offerings delivered customer-managed encryption and local staffing; others still faced parent-company jurisdiction, a material caveat for courts and regulators. Meanwhile, regional providers such as OVHcloud, T-Systems, Orange Business, Cleura, and Swisscom expanded compliance tooling, analytics services, and marketplace integrations to compete for complex workloads. The competitive axis shifted from raw feature count to provable control: who held the keys, who ran the ops, which entity answered the subpoena, and how quickly workloads could exit if obligations changed.
Trade-offs stayed unavoidable. Air-gapped or strongly sovereign environments lagged mainstream public clouds in serverless breadth, AI accelerators, and partner ecosystems. Budgets redirected to sovereignty could slow new product bets unless value streams were rebalanced. Talent constraints—security-cleared SREs, compliance engineers fluent in sectoral rules, and cloud architects who could code portability—also limited speed. Practical next steps therefore centered on a “minimum viable sovereignty” baseline that prioritized what mattered most: durable portability, auditable operations, enforceable locality, and contractual clarity. Successful programs had classified data, mapped it to placement tiers, validated exit via drills, funded capability gaps, and made sovereignty an engineering discipline rather than a slogan.