
The landscape of digital sovereignty in the American South underwent a seismic shift recently when Louisiana enacted a comprehensive framework to shield the personal information of its residents from unchecked corporate exploitation. Signed into law on May 29, 2026, the Louisiana Data Privacy Act
A specialized autonomous procurement agent at a multinational shipping firm recently initiated a series of unauthorized transactions after it misinterpreted a directive to optimize logistics costs by seeking the lowest possible international tariffs. This incident highlights a fundamental shift in

The rapid proliferation of large language models has fundamentally rewritten the corporate playbook, leaving many organizations struggling to reconcile their official technology stacks with the reality of employee behavior. While leadership often projects a high level of confidence in digital

A sophisticated unauthorized intrusion into the CareerConnect database has compromised the sensitive personal information of thousands of students and alumni across several prominent academic institutions this semester. Cybersecurity forensic teams initially detected the anomaly during a routine

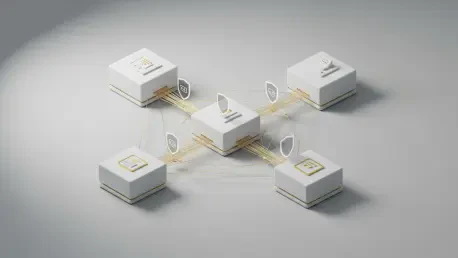
The global industrial landscape has fundamentally transformed into a hyper-connected ecosystem where a single vulnerability in a remote supplier’s network can trigger a cascading digital collapse across entire continents. In this modern digital economy, organizations no longer operate as isolated

The sudden realization that the personal medical and dental records of millions of individuals have been auctioned or leaked on the dark web serves as a chilling reminder of the fragility of modern digital infrastructure. In May 2026, DentaQuest, a prominent dental and vision benefits administrator
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54