
The rapid proliferation of large language models has presented enterprise leaders with a significant paradox, forcing Chief Information Officers to balance the immense potential of artificial intelligence against the non-negotiable mandate of data security. For years, the prevailing model required

In an unprecedented legal maneuver that sends shockwaves through the global technology sector, a prominent European trade body has formally challenged the regulatory approval of one of the largest tech acquisitions in history. The bombshell filing by the Cloud Infrastructure Services Providers in

As enterprises increasingly grapple with the intricate demands of data sovereignty and the strategic desire for greater vendor flexibility, the challenge of managing disconnected application estates across a patchwork of providers has become a significant operational bottleneck. In response to this

The rapid evolution of artificial intelligence has shifted from a theoretical exercise to a practical business imperative, and the second day of AWS re:Invent 2025 in Las Vegas made it clear that the industry is on the cusp of its next great transformation. Moving beyond the now-familiar realm of

The relentless integration of artificial intelligence into modern applications is creating a silent but profound crisis within the very systems designed to build and deploy software, forcing organizations to confront a critical vulnerability they never anticipated. This new frontier of development
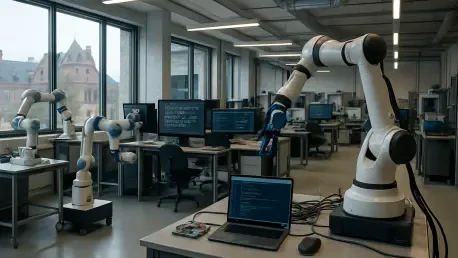
As European enterprises navigate the complex intersection of explosive AI demand and uncompromising data privacy regulations, a new model for technological independence is emerging to challenge the status quo. This movement toward sovereign AI is reshaping how businesses approach innovation,