Boards confronted a blunt reality: encryption that protected contracts, trading strategies, health records, and firmware updates could be cracked once sufficiently powerful quantum systems scaled, and the data stolen today might be decrypted before its value expired. As this threat surfaced, most enterprises discovered a blind spot—no reliable catalog of algorithms, keys, certificates, or crypto-libraries across sprawling estates, from API gateways to embedded devices. That gap turned a technical milestone into a governance test. The shift was not just swapping RSA or ECC; it involved revisiting trust anchors, policy engines, and the way applications bound to cryptographic services. For resellers, integrators, and managed service providers, the result was a client demand spike for structured discovery, hybrid migrations, and steady-state cryptographic operations that soothed risk while meeting audit timelines.
The Urgency and the Advisory Gap
Why PQC Matters Now
Practical risk arrived in plain sight. NIST advanced selections such as CRYSTALS-Kyber for key establishment and CRYSTALS-Dilithium and SPHINCS+ for signatures, and regulators mapped deprecation horizons landing roughly between 2030 and 2035. That guidance collided with “harvest now, decrypt later” operations, where adversaries lifted encrypted archives, TLS captures, and signed artifacts with the expectation of future decryption. Long-lived targets—mergers and acquisitions records, genomic datasets, industrial telemetry, and secrets in backup vaults—were especially exposed. The problem extended beyond servers. IoT devices with constrained update paths and firmware signing chains locked to P-256 or RSA-2048 could anchor systemic fragility if not addressed with hybrid or post-quantum signing options during scheduled refresh cycles.
The immediate question was how to move without breaking interoperability. TLS 1.3 remained foundational, but pilot deployments explored hybrid key exchange that combined classical ECDHE with post-quantum KEMs to retain forward secrecy while testing Kyber variants in controlled segments. Code signing pipelines began modeling dual-signature artifacts, keeping legacy verification working while introducing Dilithium for new trust paths. On the data side, storage teams prioritized re-encrypting archives and high-retention backups as KMS vendors rolled out PQC-ready interfaces and roadmap dates for hybrid wrapping keys. Public-sector programs and procurement rules accelerated action, making it feasible for channel partners to align engagements with funding windows and published milestones rather than ad hoc, tool-first experiments that risked drift.
Why This Is a Channel Moment
The sheer breadth of impact created a lane for advisory-led partners. Cryptography lived in X.509 profiles, S/MIME and SSH, service meshes, mobile apps, load balancers, and hardware security modules tied to FIPS 140-3 requirements. Few organizations owned a unified “cryptographic bill of materials” listing algorithms, key sizes, certificate chains, library versions (OpenSSL, BoringSSL, WolfSSL), and application bindings. Without discovery, prioritization was theater. Channel partners that built repeatable assessments—scanning certificate inventories, interrogating binaries for crypto APIs, and tracing data flows through message brokers and service buses—could turn chaos into a ranked migration slate with clear business impacts, RTO/RPO constraints, and vendor readiness signals that sponsored executive buy-in.
Crucially, success favored crypto-agility rather than wholesale rewrites. Partners introduced crypto-service gateways to abstract applications from HSM specifics and expose centralized policy for algorithm selection, key lifecycles, and certificate enrollment. This indirection allowed hybrid rollout: keeping ECDSA for broad compatibility while enabling Dilithium verification where supported, or routing selected microservices through hybrid TLS in blue/green deployments that measured latency impact and handshake rates. The model also translated regulatory guidance into action. For instance, critical infrastructure clients needed provable plans tied to sector directives, while financial institutions demanded audit artifacts showing inventory baselines, risk acceptance for non-upgradable endpoints, and compensating controls like envelope encryption or tokenization to mitigate harvest risks until vendor firmware caught up.
Revenue Plays Across the Transition
Assessment to Architecture
Revenue started with clarity. Readiness assessments mapped algorithms and keys, profiled libraries and protocol use, and cross-referenced data classes against retention windows and threat models. Estate-wide discovery moved beyond scanning public endpoints to include internal PKIs, mTLS within clusters, VPN concentrators, email gateways, and build systems that sign containers and mobile apps. Partners that produced defensible artifacts—asset lists, risk registers, dependency graphs, and supplier roadmaps—won the right to shape budgets. Funded pilots linked to national cybersecurity initiatives often underwrote this stage, creating momentum for broader engagements that flowed naturally into architecture and integration sprints.
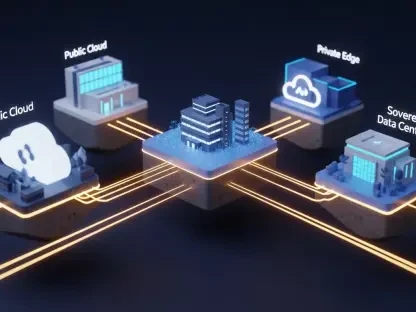
Architecture monetization followed the evidence. Crypto-service gateways delivered a backbone for policy, rotation, and telemetry, reducing app-by-app retrofits. HSM estates were rationalized, with legacy modules upgraded for FIPS 140-3 alignment and cloud KMS integrated for elasticity and regional control. Hybrid schemes emerged as the default bridge: negotiate key exchange with Kyber plus ECDHE, sign firmware with Dilithium alongside ECDSA, and support composite certificates to maintain ecosystem compatibility. Channel architects sequenced these shifts through non-disruptive patterns—sidecar proxies in service meshes, API gateway plugins for client negotiation, and staged CA updates—so applications gained agility without refactoring every cryptographic call.
Deployment to Operations
Deployment quickly bled into operations, creating durable services revenue. Managed cryptographic services took ownership of KMS, HSM clusters, crypto-gateways, certificate authorities, and policy engines, complete with SLAs, change windows, and continuous compliance reporting. Certificate lifecycle automation reduced outages from expirations, while gateway telemetry exposed where classical-only connections persisted and which partners lagged on hybrid support. For resource-constrained teams, this operating model was the only viable way to keep pace with evolving drafts, interop findings, and vendor firmware releases without derailing application roadmaps or exhausting platform teams already juggling identity and cloud security mandates.
Sector-specific packaging amplified margins. Financial buyers expected alignment to supervisory statements and stress-tested runbooks for failover of signing services. Critical infrastructure operators prioritized deterministic maintenance windows, tamper-evident logging, and offline key ceremonies. Public-sector clients required procurement-ready bundles tied to NIST selections and migration milestones, including playbooks for sensitive workloads like air-gapped environments and SCADA networks. Beyond core controls, partners modernized PKI for machine identities, refreshed OCSP responders for higher throughput, upgraded IAM and federation to support hybrid token signing, and pushed PQC-ready or hybrid TLS/VPN profiles across edge terminators, load balancers, and email security stacks. Data-at-rest programs introduced re-encryption workflows keyed by data longevity, while application teams wrapped legacy crypto with abstraction layers to insulate business logic from algorithm churn.
Execution Patterns That Win
Roadmaps, Governance, and Packaging
Winning programs started with governance that bound security intent to delivery mechanics. Roadmaps ranked systems by data half-life, dependency chains, patchability, and vendor trajectory, assigning clear owners and decision gates. Hybrid-first plans unlocked quick risk reduction—protecting new sessions and signatures—while allowing time for performance tuning and interop testing. Central policy lived in gateways and modern KMS/HSM platforms to avoid tool sprawl. Crucially, partners embedded observability: dashboards tracking algorithm distribution, certificate age, handshake outcomes, and supplier conformance transformed migrations from episodic projects into measurable programs with quarter-by-quarter progress.
Packaging did the heavy lifting in regulated sales. Audit-ready deliverables—inventory baselines, exception registers, compensating controls, and tabletop exercise reports—turned risk reduction into compliance evidence. Partners built repeatable runbooks for CA cutovers, firmware signing transitions, and composite certificate issuance, using canary stages and rollbacks to limit blast radius. Where skills were thin, alliances with specialist PKI engineers and cryptographers filled depth gaps. Cross-functional cadence mattered. Security, infrastructure, app developers, and procurement aligned through a RACI-backed rhythm that placed crypto changes within normal release trains. This operationalization kept momentum, contained change fatigue, and normalized cryptographic evolution as a platform capability rather than a one-off crisis.
Market Signals, Risks, and Mitigations
Market signals already favored early movers. NIST selections clarified procurement, public-sector pilots created reference architectures, and large vendors shipped previews of PQC-ready libraries and device firmware. Channel partners that documented interop findings—latency deltas in hybrid TLS, signature size impacts on constrained links, certificate chain behavior in legacy clients—earned trust as reality checkers, not hype vendors. Nonetheless, risks persisted. Skills were scarce, legacy systems were brittle, and suppliers advanced at uneven speeds. The mitigation pattern was consistent: repeatable frameworks, pre-production testbeds, staged rollouts with policy fallbacks, and contractual pressure that tied supplier milestones to exposure management.
By the time mature programs hit stride, the playbook had become concrete and the business case defensible. Discovery established a crypto bill of materials; governance converted it into a sequenced plan; hybrid deployments reduced immediate harvest risk; and managed services kept the substrate current without draining internal teams. Partners that invested in test harnesses, composable service catalogs, and sector-specific artifacts differentiated on execution, not slogans. The conclusion followed from evidence rather than rhetoric: acting early conferred optionality, stabilized audits, and compressed the learning curve. The next steps were clear—expand inventory depth to third-party dependencies, shift more controls into policy-driven gateways, and negotiate supplier commitments—so the transition proceeded as a controlled program, not a scramble.