The sudden compromise of the widely utilized Axios library highlights a terrifying vulnerability within the modern software development lifecycle that relies heavily on third-party dependencies. With a staggering volume of over one hundred million weekly downloads, Axios serves as a foundational element for countless web applications and Node.js environments across the globe today. The breach originated through the targeted takeover of the primary maintainer’s account on the npm registry, which granted malicious actors the authority to distribute poisoned updates directly to unsuspecting developers. Specifically, versions 1.14.1 and 0.30.3 were released with embedded malicious payloads designed to deploy a sophisticated cross-platform remote access trojan across Windows, macOS, and Linux systems. This incident underscores a critical failure in the chain of trust that governs how software is distributed, as even the most reputable packages can become vehicles for malware without any immediate signs of tampering in the repository.
Anatomy of a High-Speed Supply Chain Attack
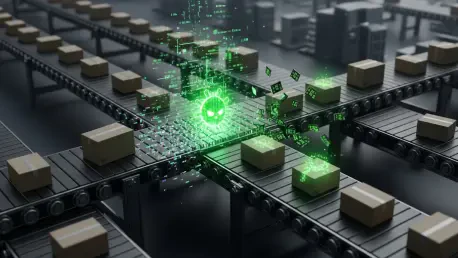
The operational maturity displayed by the threat actors in this campaign suggests a level of preparation and execution that far exceeds typical script kiddie activity or automated bot attacks. Technical analysis revealed that the malicious dependencies were meticulously staged approximately eighteen hours before the final deployment, indicating a calculated window of opportunity. Once a developer executes the standard npm install command, the embedded malware initiates communication with the attackers’ command-and-control servers within a mere two seconds of the installation process. To ensure long-term persistence while avoiding detection by traditional security software, the malware was engineered with self-cleaning capabilities that allowed it to delete its primary files and replace its own metadata with a clean version after the initial execution. This rapid-fire execution model minimizes the time defenders have to react, turning the very tools used for automation into high-speed conduits for data exfiltration.
One of the most alarming aspects of this specific breach is the tactical decision by the attackers to bypass the official GitHub repository entirely and publish the malicious code directly to the npm registry. Because standard security audits and automated scanning tools often focus on comparing local changes against the source code hosted on platforms like GitHub, this discrepancy created a massive blind spot that rendered traditional oversight ineffective. A manual review of the public source code would have shown nothing suspicious, even as the registry-hosted package was actively compromising systems worldwide. This technique exploits the inherent trust developers place in package managers, assuming that the code residing in the registry is an exact mirror of the audited source code. By breaking this link, the attackers have highlighted a fundamental weakness in the software supply chain where the distribution infrastructure itself becomes the most vulnerable point of entry for sophisticated state-sponsored groups.
Attribution and Strategic Defensive Responses
Security researchers have begun to identify patterns that point toward the involvement of the North Korean-linked threat actor known as UNC1069, an entity famous for targeting financial institutions. This group has historically focused on the theft of cryptocurrency and the infiltration of developer environments to gain lateral access to high-value corporate networks. The Axios incident is viewed as a continuation of this strategic trend, where the build pipeline is now treated as the new frontline in global cyber warfare. Instead of attempting to find zero-day vulnerabilities in hardened production environments, attackers are moving upstream to exploit the collaborative nature of open-source development. By compromising a single maintainer, they effectively gain a back door into thousands of downstream organizations, ranging from small startups to Fortune 500 companies. This shift represents a move away from brute-force attacks toward high-leverage operations that maximize the impact of a single compromise.
Following the discovery of the compromised Axios versions, organizations were forced to initiate immediate and comprehensive response protocols to mitigate potential long-term damage. Impacted hosts were promptly quarantined from the rest of the network to prevent the lateral movement of the remote access trojan, while security teams activated incident response plans to identify any signs of data exfiltration. All exposed credentials, application programming interface keys, and sensitive secrets that were accessible on the compromised machines were systematically rotated to neutralize the threat of secondary breaches. Moving forward, the focus shifted toward the implementation of more robust software bill of materials requirements and the adoption of localized package mirrors that were audited before internal distribution. These actions established a new baseline for digital integrity, emphasizing that supply chain security required continuous vigilance rather than periodic checks during the initial setup.